No more passwords in Github
If you haven’t heard yet, I’m telling you: Github1 will no longer admit passwords as an authentication method for your repositories (see their post). This change is meant to strengthen the overall security of the famous git2 platform. In this post I’ll show you how to adapt to the change.
One password to rule them all
Alright, I see that Github will impose that change but… what is the problem of having a password in Github for everything as I was doing so far?
Image: A github repository.
Pulling you repo and logging in Github
So far, you were probably logging in Github with the same password you were using to authenticating from the CLI to perform some git pull or git push. Well, this is a security risk, because you are sending your password every time you do that request. Also, most of us configure the Git client to store your password so you don’t have to retype it every time.
However, having the same password for everything and, possibly, stored in more than one device does not seem the best option. Besides, there is another problem.
Enabling a second factor authentication method
Having a second factor authentication method in Github was not very common so far. However, Github is the place where you store your private and public code, and you want to ensure maximum security regarding the access to your account. Actually, this is of utmost importance for people working on some private business code.
However, if you are using your password to access your repositories from the git CLI, how do you use your second factor? The thing is that you will not be able to. Once you adopt the change I will explain afterwards, you will be able to enable a second factor method for your account.

Image: Security key as a second factor authentication method in Github.
SSH to the rescue
SSH (Secure Shell) is the most used administration utility. It replaced the legacy telnet utility as SSH provides a secure and encrypted communication between the client and the server. It is used to connect to remote servers for their administration and for other services like sFTP (secure File Transfer Protocol).
Using SSH with Git and Github
Then… can I use SSH with git? Of course! Instead of using HTTPS as you may be doing, you will write things like:
git clone git@github.com:myusername/my-private-repo.git
Setting it up is easy. Just three steps:
- Generate a SSH key pair
- Tell Github your public key
- Clone or change your remote URL in
git
1. Generate a SSH key pair
The first step is a simple command. You are going to create a key pair and store it in your machine. Your private key will be used to authenticate yourself in github, while the public key will be copied to github (step 2). I recommend using ed25519. Here is an example:
ssh-keygen -t ed25519 -C "githubtest"
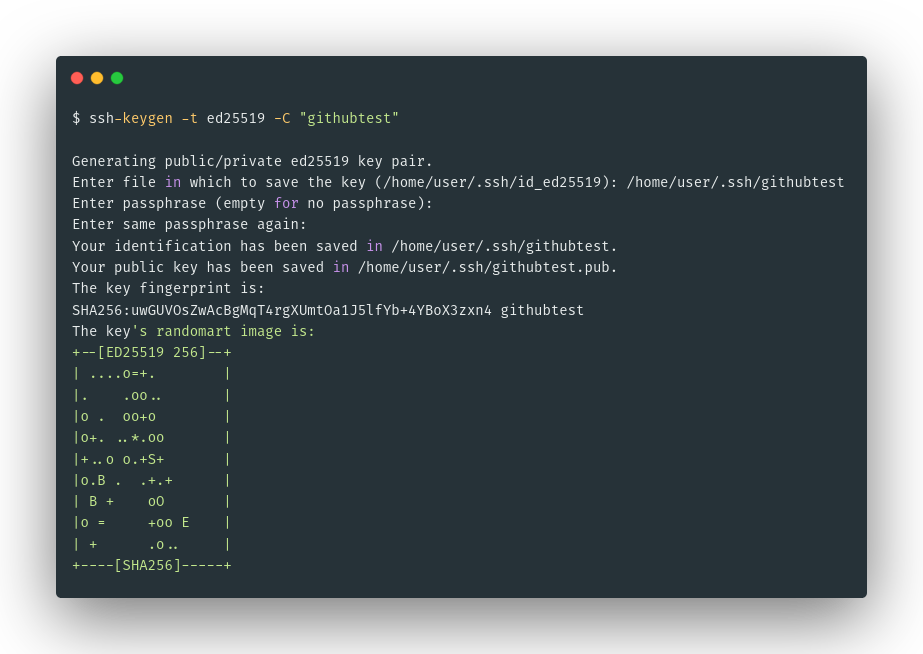
Image: First step: generate your asymmetric SSH key pair.
2. Tell Github your public key
cat ~/.ssh/githubtest.pub
After that, go to Github (https://github.com) > Settings > SSH and GPG keys > New SSH key. Now, paste the contents you copied from the previous cat and you are done!
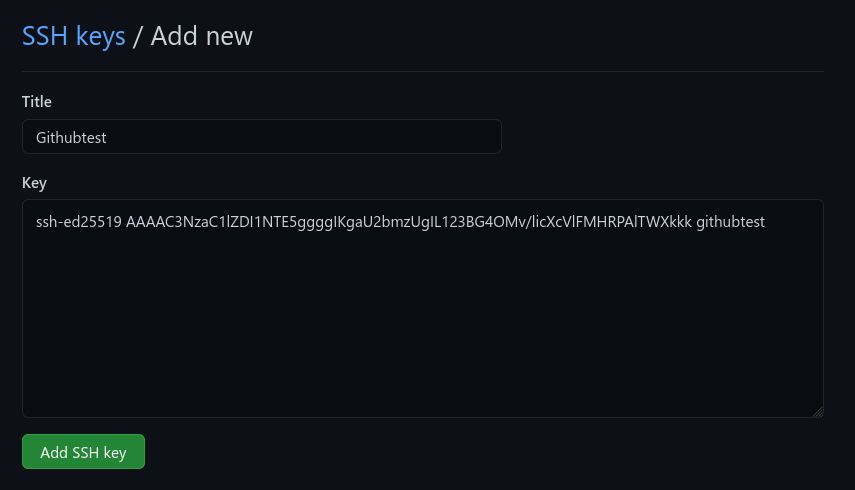
Image: Second step: copy your public key to Github.
3. Clone or change your remote URL in git
Now, it is time to test all works. You can directly clone any of your private repositories or changing your already cloned repositories to work with SSH. The following snippet lets you check that the new authentication is working and making a repo use SSH instead:
ssh -T git@github.com
cd your/existing/repo/directory
git remote set-url origin git@github.com:username/repo.git
git fetch origin master
One alternative: use tokens
If you don’t want to spend time generating SSH keys, you can also generate access tokens. Go to Github (https://github.com) > Settings > Developer settings > Personal access tokens. Now, you can use it as you would with a normal password.
- Benefits: Restricting access to some repositories and using Basic authentication with HTTPS different from your account password.
- Cons: It is not asymmetric.
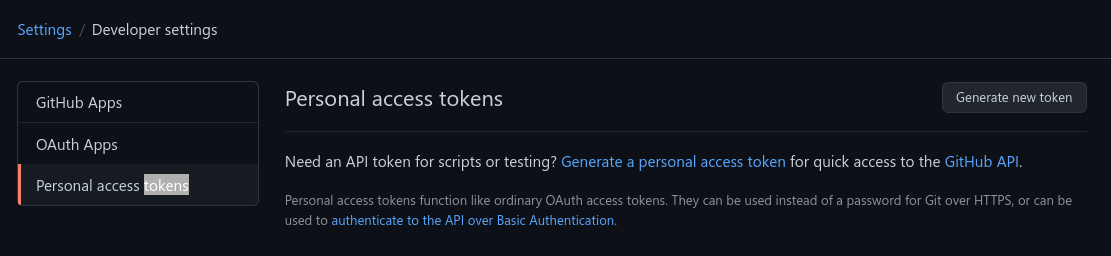
Image: Generate a Github access token for your repositories.
Extra: some useful tips for SSH
Now you use git with SSH, I’ll show you a couple of cool things about SSH.
1. Don’t retype the password every time
SSH private keys are (they should be) encrypted with a password. Therefore, every time you want to use them, you are asked for a password. How can you avoid retyping your password once and once again? With ssh-agent.
An SSH Agent keeps your private SSH keys decrypted in memory so they can be used without asking for the password every time. Use it as follows:
ssh-add ~/.ssh/githubtest
ssh-add -l
2. Use your local SSH key in a remote server
SSH does some magic sometimes. If you have a remote server where you want to use git, you can use your local computer SSH Agent to use Git in your remote server. Here’s how:
- You add your private key to the SSH Agent
- Connect to your remote server using SSH. Watch out:
ssh -A user@remoteip - Use git CLI with SSH
Conclusion
As you see, sometimes when we are forced to update to a better alternative is a pain, but it results in a more secure way of working. In this case, at least for me, it also resulted in a better experience as I learned how to avoid retyping the password each time!
Obri! Thank you for reading, this is already the 5th article of the #52challenge!
-
Github is a platform that programmers use for saving their code. Most of them, save it publicly so it can be read (and used) by other programmers. This is called (Free and) Open Source software. ↩︎
-
Git is a tool used by programmers to control versions of their software code. When they perform changes, they use git to keep track of them for the future. Github is a platform that uses git to save the code and allow others to contribute to your code. ↩︎